Flowtriq: Sub-Second DDoS Shield for AI Workloads
Quick Comparison Table...
Sub-second shields vs mega scrubbers: where Flowtriq fits in the DDoS arms race
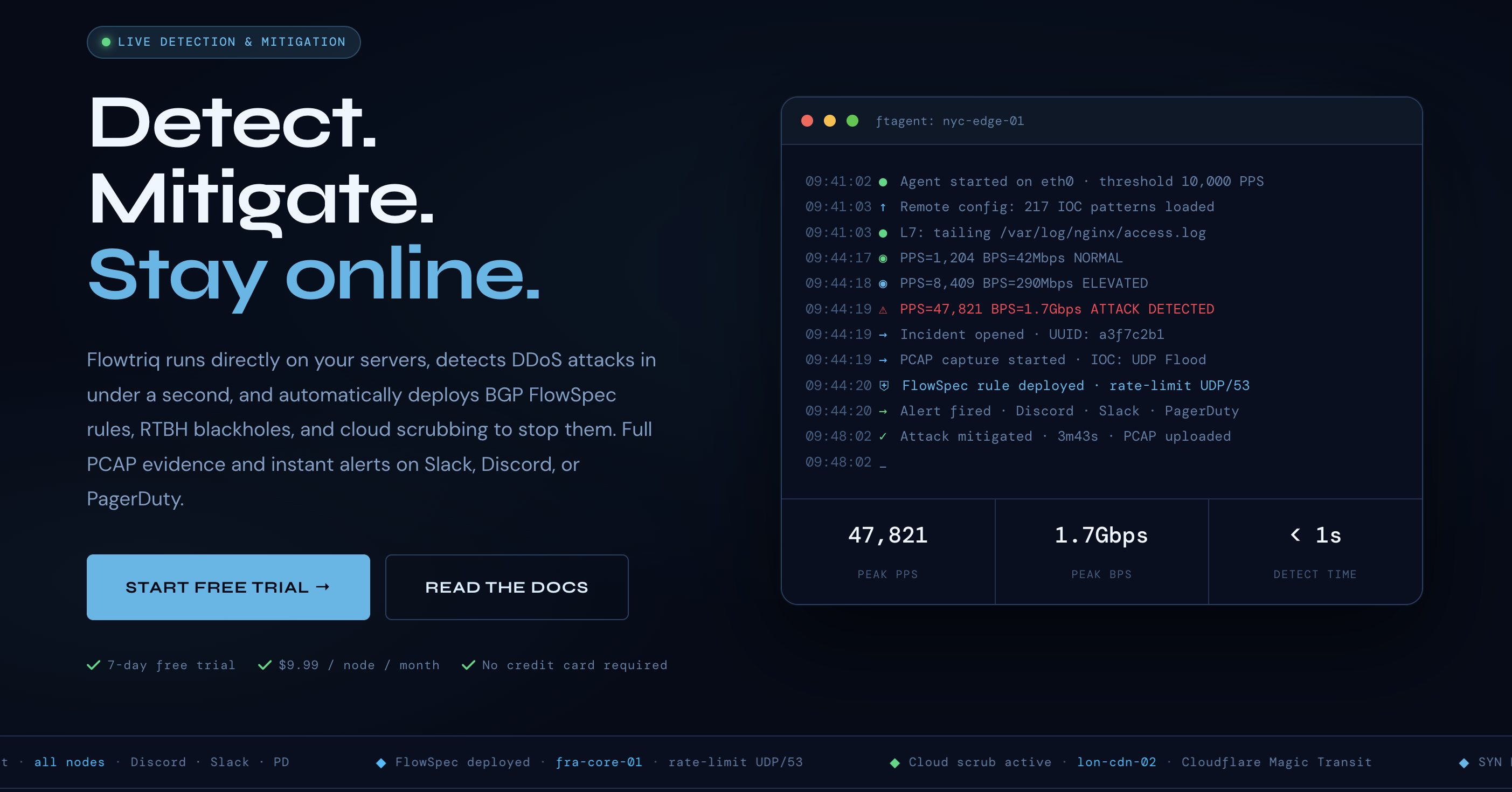
Stat hook: In 2023, Google Cloud reported a 398 million requests-per-second DDoS attack exploiting HTTP/2 Rapid Reset—yes, million RPS. That's the kind of chaos that turns LLM APIs into very expensive paperweights. Enter Flowtriq (https://flowtriq.com), a lightweight, agent-based platform promising sub-second detection and automatic mitigation right on your Linux boxes. I spent time comparing it to the big scrubbing heavyweights to see where it actually shines for AI infra teams who can't afford jitter or downtime.
Quick Comparison Table
| Feature | Flowtriq | Cloudflare Magic Transit | Akamai Prolexic |
|---|---|---|---|
| Pricing | $9.99/node/month (or $7.99 annual); flat, no traffic surcharges | Enterprise, contract-based; traffic/egress-driven | Enterprise, contract-based; bandwidth commitments |
| Ease of Use | 2-minute Linux agent, auto-baselining; no manual thresholds | Requires BGP/GRE setup, routing changes, coordination | Requires BGP/GRE setup; onboarding with SOC |
| Artificial Intelligence Features | Dynamic baseline learning, per-second anomaly detection, IOC correlation; attack profiles | Cloud ML-driven detection in scrubbing centers; opaque tuning | Adaptive detection + global threat intel; operator-managed |
| Integration Options | BGP FlowSpec, RTBH, Cloudflare Magic Transit, OVH VAC, Hetzner; Discord/Slack/PagerDuty/OpsGenie/SMS/email/webhooks | Magic Firewall, Spectrum; SIEM/webhooks; global anycast | GRE tunnels, SIEM integrations, SOC workflows |
Where Flowtriq Wins
- ○Sub-second, on-box detection for latency-sensitive AI APIs. When your LLM inference nodes are juggling tokens and tight SLOs, every millisecond counts. Flowtriq's ftagent sits on the NIC, learns baselines, and trips mitigations in under a second. In my experience, that's a lifesaver compared to waiting for traffic to hairpin through Cloudflare Magic Transit or Akamai Prolexic before you even classify the blast.
- ○Transparent pricing that scales with nodes, not traffic. $9.99 per node with no "gotcha" egress or clean-pipes overages is refreshingly simple. If you're a startup hosting GPUs across Hetzner/OVH and running cost models in a spreadsheet (been there, added too many conditional formats), this is easier to forecast than enterprise scrubbing contracts.
- ○Automated forensics without extra tooling. Full PCAP capture triggered on every attack, immutable audit logs, and IOC correlation against 642k+ indicators make post-incident reviews sane. I've lost weekends hunting down odd spikes; having packet captures and attack profiles auto-attached to alerts is the kind of ops candy most cloud scrubbing vendors don't hand you directly.
Where Competitors Have an Edge
- ○Absorbing truly massive volumetrics. If you're facing multi-Tbps floods across entire IP ranges, the global capacity and anycast reach of Cloudflare Magic Transit and Akamai Prolexic is hard to beat. Their scale is the point. See user feedback on Cloudflare (G2 reviews) and Akamai (G2 reviews).
- ○Whole-network protection and compliance posture. Need defense for legacy appliances, Windows servers, and MPLS backbones with strict SLAs and 24/7 SOC escalation? The big providers bring mature playbooks, certifications, and exec-friendly guarantees that your auditor will actually recognize.
- ○No-agent architecture. If agents are a non-starter for policy or performance reasons (some HPC shops are allergic), routing-based scrubbing is cleaner operationally—once you get over the BGP hump.
Best Use Cases for Artificial Intelligence
Choose Flowtriq when:
- ○You run Linux-based LLM inference, RAG services, or vector DBs on bare metal/VPS, and latency spikes are unacceptable.
- ○You want automatic, per-node detection with playbook-driven mitigations (BGP FlowSpec, RTBH, or escalations to Cloudflare/OVH/Hetzner) without hand-tuning thresholds.
- ○Your team lives in Slack and PagerDuty and wants alerts that route automatically without building custom webhook glue.
- ○You need forensic-grade PCAP captures and immutable logs for compliance or post-incident review.
Choose Cloudflare Magic Transit or Akamai Prolexic when:
- ○You're absorbing multi-Tbps volumetric floods across entire ASNs and need global scrubbing capacity.
- ○You require enterprise SLAs, SOC escalation, and compliance certifications your auditor will recognize.
- ○Your network architecture makes agent deployment impractical or against policy.
The Verdict
For AI infrastructure teams running latency-sensitive workloads on Linux — inference nodes, vector DBs, RAG pipelines — Flowtriq is the most operationally practical first line of defense available today. The sub-second detection window, flat-rate pricing, and automated forensics fill a gap the big scrubbing vendors either can't or won't address at this price point.
It's not a replacement for Cloudflare or Akamai at massive volumetric scale. It's a complement — fast, cheap, and surgical where they're broad and expensive. For most AI teams, that's exactly the tool missing from the stack. Start with the 7-day free trial on your most exposed node and let the baseline data tell you the rest.
External Reference
Visit Flowtriq →